Wazuh : Security Information and Event Management (SIEM) for Small and Medium-Sized Enterprises
Abstract
One of the greater risks associated with significant growth and use of Information Technology interwoven with the internet is Cybercrime. An alarming increase in cyber-criminal activity over the years has forced organisations to take defensive measures and always use up to date technologies for the same purpose. The current developments show that SMEs (Small and Medium Enterprises) are the most vulnerable entities to cybersecurity threats and attacks. This research states various security related challenges that the SMEs have to face today with an agenda to raise awareness about how critical it is to deal with them and avoid the consequences.
Our research investigates the SIEM which currently being used in the Small and Medium Enterprise’s. The Wazuh SIEM is an open source SIEM which can be used by any of the SME’s due to its low cost and higher availability for the end points as it can be scaled horizontally. There are many SIEM’s present in the market such as Q Radar, Splunk etc, but they are highly expensive, their services can’t be purchased by any SME’s.
1. Introduction
This Chapter begins with the introduction of security challenges faced by Small and Medium Enterprises (SME’s) while building their IT infrastructure and why its necessary to deploy a Security Information and Event Management (SIEM) tool.
It goes on to explain what SIEM tools typically do and how they function with the help of a security platform, Wazuh consequently which will define the problem for this report. Subsequent sections of the chapter will talk about what we are hoping to achieve from the research, mainly the aims and objectives followed by a brief outline of the artifact, a documented demonstration of Wazuh fully deployed on Windows in a custom environment and finally closing with the structure of the report.
1.1 Security Issues faced by Small and Medium Sized Enterprises
As reported by leading global information services organisations like Experian, there is a year-on-year increase in the number of crafty data breaches. SME’s face bigger challenges with the constraints that come with their smaller size — limited finances, weaker planning, lesser operational control, inadequate staff training and slower deployment of information systems. A prolonged lack of resources puts these organisations in an even more vulnerable position since its highly problematic to detect them beforehand let alone prepare for these attacks. This is the principal reason that renders SMEs’ the primary target for cyber attackers. Therefore, it is essential that they learn how to plan, respond and recover in event of security breaches.
Recognising the need for a response system towards increasing cyber threats, some standards and guidelines have been issued to inform organisations of event responses. However, these are rather widespread and generalised. For example, a security data breach management guide by ICO talks about having technical and non-technical employees aid in developing recovery strategies, referring to HR and IT teams; another example is the Experian guide for security data breaches which keeps referring to the upper management dealing with these events and same with the guide published by the Government (Data Breach Response Checklist) suggesting a response team from Human Resources. While some of these may be applicable and useful for large organisations, they are not practical for SME’s to implement as most of the organisations operate with a small number of employees. Even though falling prey to cyber-attacks poses a risk as huge as bankruptcy, small organisations are simply unable to hire additional staff to effectively deal with the security issues and with financial constraints, cannot outsource it to a third party. This only leaves them with the option to build and deploy a system in-house which gives rise to another challenge. While developing an in-house response system, SME’s do not implement enough security strategies for different network components and today with smartphones, netbooks, tablets, IT security is changing at a fast pace putting smaller enterprises in a weaker position. Although there are many systems available to shield enterprise network; for example — firewall, anti-virus systems and IDS, they all function independently of each other. Many attacks are recognized only if events and logs of distinct security components are correlated and combined. This is possible with a security information and event management (SIEM) system that can resolve a lot of the above issues but nowadays these systems are overly complicated and costly to deploy and maintain. We will further elaborate on this in the upcoming chapters.
Another issue that SMEs are facing is that of compliance obligations and other governmental regulations such as SOX, PCI, HIPAA, ISO27000–03, etc. failing the maintenance of which might result in heavy losses in business, employees and hefty fines. To avoid these many enterprises regularly conduct internal audits confirming and certifying that these requirements are being met. This is also an area that SIEM tools can fully manage for the enterprise.
1.2 Security Information and Event Management (SIEM) tool for SMEs
SIEM is a security system that comprises complex technologies that function together to provide a centralised understanding of an infrastructure, covering all its bases. SIEM solutions are systems capable of gathering information from network and security devices, identifying and evaluating security events in real-time including long-term log storage, trend analysis and historical reporting. SIEM is a combination of two technologies, namely, SIM (Security Information Management) and SEM (Security Event Management). The former area provides long standing storage, reporting and evaluation of log data. The latter area provides real-time checking, correlation of events, console views and reports. For setting up a SIEM system, both can be merged in a suitable way to the organisation.
SIEM tool gives information security function an all-inclusive view of any exposure to security breaches through the accumulation of log data from numerous sources, for instance switches, proxy servers, firewalls, web server logs and load balancers; correlation of the obtained logs to extract intelligence and make sense of the mass data; notifying when particular event conditions are encountered; and a single overall dashboard that provides visibility to events that formerly may have required management of reporting tools and multiple dashboards.
These grouped systems of complex technologies have now become a key element of organisation networks and IT infrastructures as it allows the organisation to merge and evaluate messages and alerts of individual components of an Information Technology system while considering messages of specialised security systems like VPN gateways and firewall logs as well. They essentially act as incident warning mechanisms that correlate threat data and vulnerability to provide insight into risk prediction, prioritising these risks along with reporting and log auditing for compliance purposes.
In a more detailed version, technology used in SIEM offers close to real-time analysis of security alerts/breaches that have been created by network applications and hardware. SIEM can be used as a managed service, software or appliance. It also generates reports for compliance purposes from log security data. The main purpose of SIEM is to help enterprises respond to threats/attacks faster and organise heaps of log data. One of the key focus is to help managing and monitor directory services, user and service privileges and other system configuration changes, as well as providing log audit assessment and incident response. Not every SIEM system available in the market has all the features however a thorough SIEM system consists of some different segments, which must support the following functionalities:
· Event Correlation — normalise, correlate, save and archive log files to a common database for additional evaluation
· Identity Mapping — allocating network specific info like IP or Mac addresses to real identities, for example the genuine user
· Compliance Reporting — constant check on IT compliance i.e., risk, integrity, effectiveness, of an organisation and comparing it to the actual situation
· Application Programming Interface — providing a standard interface for the integration of arbitrary devices/systems and adaptation of legacy security systems
· Situation Detection — detection of unwanted/unexpected situations and surveillance of the network condition. This can consist of managing configuration or anomaly detection methods.
· Key Performance Indication — measurement of IT security by analysis of asset details involving security data
· Rule Based Access Control — central picture of all events of an enterprise under observation of distinct responsibilities
The implementation of SIEMs in a variety of contexts ranges from industrial control systems for critical infrastructure to large scale enterprises with multiple security domains to administer. There is one context of specific interest which is that of SIEM implementation (Miller et al., 2011) in small and medium sized enterprises as the practice has revealed that these systems are extremely complex and only possible with sizeable personnel effort involving certain technical skillset although this is only true to some extent, there are multiple SIEM tools that offer support and can be easily deployed and operated by personnel with basic technical skills. It has also been seen that many times these systems are installed but neglected in ongoing operation which is where businesses fail to extract maximum benefit from these tools. However, despite all this, there has been rapid growth in the adoption (Fink D, 1998, pp. 243–253) of SIEM hugely driven by the following reasons:
· Event logging demands for Payments Card Industry code of compliance.
· Other mandatory compliance responsibilities — FISMA, NERC, PII, SOX, HIPAA
· Obtention and retention of certifications — ISO 27000 to ISO 27003
· Policy violation and policy enforcement validation
· Ticketing systems
1.3 State of Problem
There are several cybersecurity issues faced by small and medium sized enterprises presently. Due to limited resources, these organisations become prey to cyber-attacks, internal and external. The lack of research in this area in addition to a serious lack of technical knowledge and know-how makes it almost impossible for them to effectively prepare for and tackle any incidents. Due to this reason, SMEs are increasingly becoming the prime target for phishing/spear phishing, DDOS attacks, malware attacks, SQL injection and other such cyber-attacks. These crimes can cause serious damage to a relatively new organisation’s reputation and incur the loss of assets, employees and capital. To make the situation worse, in the event of a security breach, legal actions can also be undertaken resulting in a fine up to the amount as large as 4 percent of the annual turnover. Small businesses conduct regular in-house audits requiring extra personnel to prevent this from happening to burn a hole in their pockets.
All the solutions and guidelines provided for cybersecurity management are more applicable to large scale businesses and impracticable for small businesses to embrace. Nevertheless, the research conducted here will offer an all-round solution to the problems discussed above.
1.4 Defining the Aim and Objectives
1.1.1 Aim of Research
To materialise and validate that SIEM technology is the best suited solution to cyber security problems faced by the SMEs with the help of an actual working tool, Wazuh which is not only feasible but also effective, easy to implement and can be adjusted according to requirements of any small/medium scale environment (O. Podzins and A. Romanovs, pp. 1–5).
1.1.2 Objectives
We will achieve the aim of the research project with the help of Wazuh, an open source SIEM (K. Detken et al., 2015, pp. 322–327.) Tool by:
· Demonstrating the installation of Wazuh and the full deployment of all its components using Windows
· Creating a working custom Wazuh environment with documentation of its functioning
· Survey point
It is expected that from the findings of this report SMEs will have a better grasp of how SIEM technologies actually function and also how to operate them efficiently to their benefit.
1.5 Structure of the report
The first chapter introduces the reader to issues and challenges faced by SMEs in context of cybersecurity followed by an overview of the proposed solution, SIEM technology. It sets out the aims and objectives this report hopes to accomplish.
The second chapter is an outline of all the existing research on SIEM design and implementation and Security issues in SMEs over the years. It also analyses other solutions offered by previous research evaluating scope for future use.
The third chapter states the research method and process followed to achieve the main goal.
The fourth chapter talks about the survey that was undertaken by cybersecurity professionals to find out the current scenario around our problem. It reveals the results and interpretations of the survey.
The fifth chapter introduces Wazuh, the SIEM tool explaining why it has been selected as a solution followed by a demonstration of its installation and functioning within a custom environment.
The last chapter concludes with an evaluation of Wazuh’s performance and ability to help SMEs solve their security issues.
2. Literature Review
This chapter begins with a detailed account of process that was followed while choosing relevant data and research for the purpose of this report. Followed by a re-evaluation of prevalent studies that are mainly about Information security issues, current scenario in SMEs, design and implementation of SIEM (Gartner Inc. 2012) tools specific to SMEs. Finally it will give us an understanding of how useful the research can be for further development.
2.1 Methodology of Literature Review
This literature review follows Okoli and Schabram’s (2010) guidelines, which proposes an 8 step academically thorough, organized, and reiterative literature review procedure. The literature pursuit began with a broad goal in mind: to find some articles or academic papers linked to SIEMs. The Lulea University Library, Google Scholar and ProQuest are only a few examples of helpful resources.
The literature quest began with a broad aim in mind: to find some articles or academic papers that give a general overview of SIEMS as a tool and security issues faced by organisations all over the world. Google Scholar, The Lulea University Library and ProQuest were used as resources. The range was then narrowed to also include research relevant to the design and deployment of a SIEM in the sense of a small to medium-sized enterprise.
Although this paper cites a variety of secondary and tertiary sources of literature related to SIEM research, primary sources or first-hand accounts of research, contained in peer-reviewed scholarly journal articles were preferred.
After finding suitable posts, a backwards search of the references, referenced in the article was conducted, followed by a Google Scholar forward search to locate articles or papers referencing the initial article found. Academic journal papers were reported for further screening. The search was halted when it became apparent that no new papers were readily recognisable, and the study progressed to the ‘screening for inclusion’ level. After which, each of these were assessed on the basis of quality, general result application, research method and relevance to the particular topic of our interest.
Post that, the research studies were revisited, and a data compilation form for each paper was finished. This section gathered the research’s intent and contribution, why it was relevant, the result, the context, any potential research suggestions, and any helpful comments (based on observations or interesting findings). The information gathered was compiled, analysed, and the report that follows was written.
2.2 Prevailing Research: Understanding and Analysis
The research from the chosen papers/articles that has been talked about in this chapter are mainly centred around three topics, information security challenges faced by organisations around the world, design and implementation of a SIEM tool, different models suggested as solutions to overcome the challenges faced by SMEs. These have mostly been published or written in the years 2004 through 2018.
There is much evidence in various studies conducted over the last decade of problems being faced by SME’s regarding information security management which is a component of the overall organisation management system that serves as the foundation for managing security risks, with the goal of establishing, implementing, operating, monitoring, reviewing, and maintaining the system. According to a combined survey undertaken by San Diego State University and University of Plymouth UK in 2004, there was clear evidence of security issues faced by small and medium enterprises and that only 15% of total SMEs in the UK and US had allocated a budget (G. W. P. Chamiekara et al., 2017, pp. 100–105) to security for the prevention and management of these issues due to lack of resources and knowledge. It is important to note that even after 16 years of awareness of these issues, still the SMEs are not only facing similar problems, but additional issues have been observed in more recent studies which is a cause of major concern. According to Hau et al. (2016), most businesses are unaware that they have been hacked for months. According to FireEye (2016), most businesses did not realise they had been hacked for months (469 days on average since the incident after detection). According to FireEye (2016), while the media focuses on data breaches at large enterprises, 77 percent of cybercrime is directed at small and medium-sized businesses. Despite the fact that SMEs account for 77% of cybercrime, 58 percent of SME managers do not consider cyber-attacks to be a significant danger, and 65% of SMEs do not have a security policy, small and medium-sized businesses report only 10% of computer offences to the police.
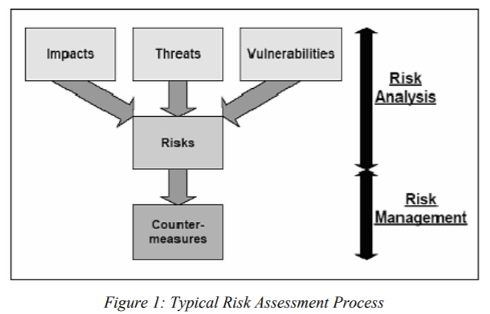
While searching for relative information, we found that most studies surrounding this area have suggested frameworks to cope up with the situation especially with the financial constraints SMEs have, one feasible solution can be an internal action procedure delegated to suitable personnel with adequate or inadequate knowledge. The combined study by UK and US proposes that Risk Assessment is step zero for counteracting these problems. The proper assessment of the risks to which a system is exposed is a critical step in determining adequate security for it. Without this, an organisation cannot be certain that it has a proper understanding of the threats and vulnerabilities that face its assets, and any existing countermeasures may be questioned. Risk Assessment entails steps such as identifying assets that need to be protected as well as threats and vulnerabilities that may be associated with those assets. Following that is the risk management process, which entails identifying, selecting, and implementing countermeasures that are intended to reduce the identified levels of risk to appropriate levels, thus managing, reducing, and possibly eliminating the recognised security risks at a reasonable cost. Despite the fact that the value and relevance of risk assessments are widely recognised, surveys show that a large percentage of businesses do not conduct any risk assessments at all, especially SMEs as it poses the threat of disrupting management and all employee activities all through its duration.
A study by University of Entrepreneurship and Law, Prague and Pan-European University, Slovakia has scientifically deduced four factors that are vital for the success of information security measures in any organisation:
I. Security controls
II. Compliance of information security management with the company’s business activities
III. Organisational awareness
IV. Top management Support
The results of their research show that Security Controls, which include procedural and technological information security controls, risk management are the most critical factors in the success of information security management. The support of top management is the second most vital factor. In the short term, organisational awareness is the most apparent and significant factor for information security management accomplishment and also SMEs should boost organisational awareness in information security management, along with the application of security controls at the first line of defence, in order to defend information, which is the company’s most valuable asset.
There has been some attention in the academic literature on incident handling in SMEs. Despite this step forward, concrete research has yet to produce a broadly accepted SME-specific incident response framework. The government, Industry and academia have all produced incident response frameworks and guides. Most define the phases of incident response as follows:
i. Preparation: the first step, which includes organisations creating or preparing an internal information security incident response team in advance of an incident (CSIRT).
ii. Verification: defined as the detection or reporting of security events within a business, containment may include isolating systems, changing passwords, and disabling accounts, depending on the vulnerability that was exploited.
iii. Eradication: Organizations seek to eliminate the components of an incident with an emphasis on system reconstruction through tasks such as detecting affected hosts, conducting malware and forensics analysis, and so on.
iv. Recovery: Entails activities such as constant testing and checking, as well as the use of backups, to get systems back online.
v. Follow-up: An activity such as conducting a post-incident meeting to review the actions taken and assess their effectiveness. The establishment of new controls, processes, and policies should feedback into organisational processes.
The study, however, acknowledges practically when challenges arise it is difficult to follow all these steps. In further chapters, it will become clear how SIEM technology automatically follows these steps making it easier for the organisation to manage incidents.
(Kapoor et al., 2018, pp. 13–20) selected personnel from SMEs were interviewed and it was discovered that in case of any incident report organisations have somewhat a similar response procedure as mentioned above which can be attributed to the rising prominence of increasing data breaches in media. However, the interview results also discovered that there was an over-emphasis on technical measures but no emphasis on their implementation or extra training or preparation which leads to an ineffective response mechanism causing the same problems to rise on loop. These findings show that while companies have incident response plans in place, they aren’t well-established in practice. Even though existing studies show how organisations struggle to put theory into practice at each stage of the incident response process, this study confirms that these patterns persist throughout the entire breach response process. Hence the need for an all-round solution is crucial at this point for the survival of SMEs as these issues only seem to be growing over the years as technology advances.
After careful reflection, it was seen that a lot of literature around the subject area was specific to SIEM design and implementation. There were a few common themes identified among these which are explained below:
Subject 1 — The design and application of SIEMs in terms of large-scale deployments and certain types of industries, especially critical systems infrastructure.
The work done by Coppolino et al. (2011) is mostly revolves around the architecture of the SIEMs solutions for the large business environments who have humongous system infrastructure, extending it to the framework of the SIEM to the security devices which includes the SCADA systems as well.
Subject 2 — The application of distinct techniques for greater understanding and analysis into the collected data, more often than not techniques from alternative fields for example data mining tools or Business Intelligence solutions
Gabriel et al. (2009) applies data mining techniques to SIEM logs to detect concealed patterns of malware activity, and Hadziosmanovic et al. (2012) propose a semi-automated log-mining design for SCADA logs in the second area of SIEM research.
Subject 3 — SIEMs are designed and implemented across heterogeneous systems and application networks, distributed computing environments , and even the integration of physical security systems and information technology systems into a single SIEM.
(Kufel et al., 2013, pp. 36–43) recommend some viable methods for SIEM implementation across email, finance, HR, and portal systems, and Sohn et al. (2012) suggest a SIEM structure that incorporates physical and IT security events for a converged view of security-related activity within an organisation.
Subject 4 — SIEM designs with novel characteristics that may be applicable to all SIEMs, such as automation (Montesino et al., 2012, pp. 248–263) of security controls relevant to the ISO 27000 or niche SIEM designs, such as a SIEM design for digital forensics or NIST series of security standards.
The last category of contemporary SIEM design includes the use of SIEMs to meet the compliance requirements of security standards such as ISO 27001, with (Metzger et al., 2011) recommending a SIEM to support ISO 27001-compliant incident management and describing a SIEM framework that allows the automation of ISO 27001 security controls for reduced complexity and greater effectiveness.
The MASSIF (or Management of Security Information and Events in Service Infrastructures) project, funded by the European Commission, aims to develop a new generation of SIEMs applicable to Olympic Games security, mobile-phone money transfer systems, SIEM challenges in distributed computing environments, and SIEMs for critical infrastructure. This project is explicitly promoting sound SIEM research, especially in these four particular areas.
These earlier studies used Design Research as their primary research technique, with designs validated through prototyping and experimental system testing. Apart from Metzger et al design’s (2011) which has been effectively applied in a real-world situation for one year, the studied designs have not been implemented in their planned contexts, and no learning from the implementation has been documented, potentially necessitating a re-design. These provide few details about the problems or expertise gained from the design’s implementation.
Several of the papers do not base their design science on any natural science theory.
Now this makes it more clear as to why the research existing since all these years has not been rewarding in solving the issues faced by SMEs. Additionally, there are no studies that specifically address the design of a SIEM in the context of a small business. Some of the earlier generic SIEM Design Principles may be useful to a SIEM designer in the SME context, but there seems to be no study in this area. However, there have been recent studies suggesting the development and the design of solutions somewhat similar to a SIEM specifically for SMEs which will be discussed in the upcoming section.
The study by Prof. Dr. K.-O. Detken, T. Rix, Prof. Dr. C. Kleiner, B. Hellmann, L. Renners proposes a model based on the architecture remarkably similar to SIEM called The SIMU project.
There can be many reasons that why SIEM may not be suitable for the SME’s environment. Some of the reason are as follows:
· The installation cost of SIEM is higher for the organisation if they are using Splunk, Qradar etc. The most time consuming process is of the configuration of the end points.
· Since the SIEM cannot be run by any person, hence, an expert with the required technical expertise is required to create the rules and troubleshoot the errors if the SIEM runs into any problem. Multiple dashboards has to be created to analyse the parsed logs from the SIEM
The focus of the SIMU projects is to create a system which is very similar to SIEM, but SIMU will enhance the security of the organisation without the complications of the SIEM. The SIMU offer better and easier integration to the organisation’s infrastructure, leading to easier maintenance and the visibility of the logs in the organisation’s network. The basic working of SIMU is just like any other SIEM meaning that it will process all the logs (Karlzen, H.,2009)and do corelation of it, detect all the events from the organisation’s network. Just like SIEM, all the measure is being process in real time.
The study claims that this model will be a better fit in the context of SME environment however one could argue that this project is still under development and in the initial funding stages and it may take years to build upon successfully and make organisations aware of its’ operations. Secondly, the architecture is only partially helping SME security issue as there is no clear evidence supporting it will help with compliance regulations which is one of the major reasons many organisations even choose to implement a security and event management tool.
As far as the main goal of this report is concerned, it is very clear from the above literature review that it is not enough to just find a solution and present it theoretically or a business monitoring framework that will help mitigate the risks involved in IT security. SMEs need more awareness about these tools available to them free of cost, a step by step guide on how to implement them and more importantly how to continue making use of them in this dynamic environment. Hopefully this report will be able to achieve this and provide scope and inspiration for further research.
3. Research Design
This section lays out the methodology, procedure and the rationale behind selecting the specific approach used to carry out this research project.
3.1 Research Process and Method Description
For the purpose of this professional research, we have undertaken a descriptive research design which explores a specific problem and the best solution possible.(Gordon, S., 2010). It begins with a survey collecting primary information and from the findings of that survey, it goes on to propose a documented solution.
3.1.1 Questionnaire
The questionnaire is designed to give us an insight into the current situation of information security management within various organisations. The data collected through this survey will support our problem statement and also validate the need for the development that follows the results.
Our sample size for the questionnaire was 35 out of which we have received 28 responses. The target population for the sample was people working in the IT department of any organisation with direct experience in cybersecurity. The sample size remained small as the questionnaire required a certain understanding of the current scenario that comes with technical knowledge and years of experience.
3.1.2 Artifact Development, Testing and Evaluation
The survey is followed by a proposed end to end solution to the problems laid out in the report. The process of development begins with a description of tool that has been selected to create the artifact, requirements for its installation and integration followed by documented installation and integration of the tool with a network. Next steps are to create a documented custom working environment with the application of certain rules that test the functioning of the technology and finally ends with an evaluation of performance and ways to improve any inefficiencies.
3.1.3 Rationale for the Selected Method
A descriptive research was found to be most suitable for the purpose of this report due to the limitations of previous literature talked about in the second chapter. The central problem this report is addressing was identified more than a decade ago and is only increasing year on year. It is paramount to take a different approach to create awareness of easily employable solutions which we hope can be achieved by way of this report.
4. Primary Research
This section provides all the details regarding the questionnaire, how the primary data was collected and survey, in what way has the survey been carried out ending with the results and its assessment.
Interview participants selection
The process of data selection is very important as it will contribute to our research. Hence, the participants for our research was chosen very carefully. The process of choosing the participants was very long as all the process was done with the help of the internet. We searched for the Small and the Medium enterprises in the UK
When we have identified the SME’s, further segregation was made on the basis of the SME’s are using SIEM or not. As per Creswell (2012, p. 206), the purpose of the qualitative research “is not to generalize to a population, but to develop an in-depth exploration of a central phenomenon”. That being said, we have chosen the organisation from the list randomly, the major reason for sampling the cybersecurity professional were to find the behaviour and the perception of the people around the SIEM technology.
4.1 Building Questionnaire and Gathering Information
In the context of the identified problem for this report, the questionnaire was created with an aim to get an insight into the information security management problems faced by SMEs presently and whether they have any kind of knowledge about the selected solution we can further build upon.
The data was collected by formally reaching out to target population through mail since direct contact was not possible under COVID situation.
4.2 Survey Results
Question 1: What is the size of organisation you are working for?
The results show that our sample is a mix of all sizes of organisation hence, there is no bias of opinion and the results are not directed one way.
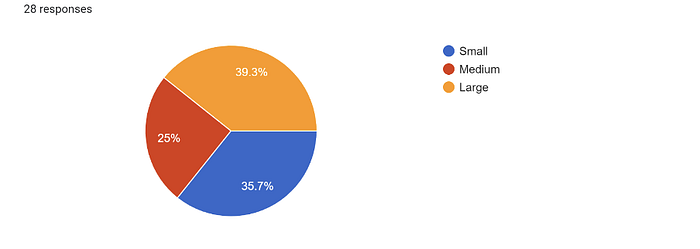
Figure 2 : Showing the mix of organisation the people work for that is Small, Medium or Large business
Question 2: Has your company ever faced any cyber security threats or attacks?
It is very clear from above that irrespective of the size of organisation, most of the organisations today have faced security threats and attacks and the need for a solution is vital.
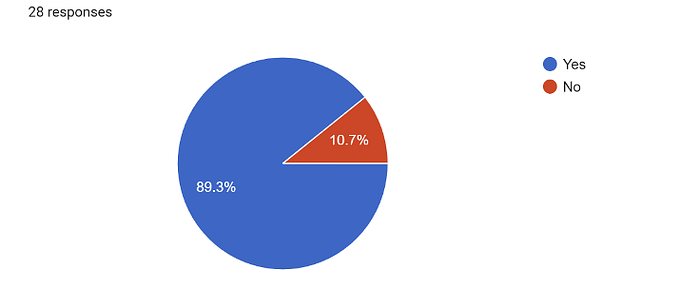
Figure 3 : Showing cybersecurity threat ever faced by the organisation
Question 3: Does your organisation currently employ a SIEM solution?
Most of the large organisations employ a SIEM solution so the one-fifth left are made up mostly of small and medium enterprises. With more than one-fifth of organisations not employing a solution, its unclear how they respond in case of an incident. But it is interesting that even with approximately 80% of the organisations employing a solution, reports show an ever-increasing rise in attacks and losses incurred on account of these attacks.
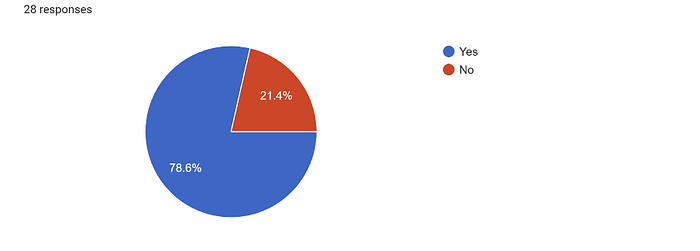
Figure 4 : Depicting how many organisation deploy a SIEM solution
Question 4: If yes, what type of solution is it?
Out of the 80% organisation that employ SIEM, most of them are using open source and just 10% have a homegrown solution. It can be seen from the responses that mostly large organisations can afford to take a commercial solution. Amongst SMEs, an open source solution is the more popular one.

Figure 5 : Organisations using different types of SIEM solution
Question 5: Is it expensive to deploy a Security monitoring and response solution?
It is evident that regardless of any situation from above, almost all the respondents think it is expensive to deploy a SIEM solution. Commercial solutions as name suggests are expensive but here it’s interesting that even organisations using an open source solution find it expensive On further inspection it was found that many tools while claiming to be open source actually have a limitation on the usage of various technologies past which certain amount or subscription becomes necessary.
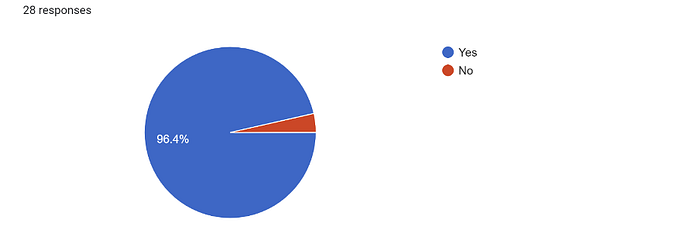
Figure 6 : Depicting whether cybersecurity SIEM is expensive or not.
Question 6: How many years of experience do you have in the field of cyber security working with Security monitoring and response solution?
It is observed that almost all large organisations have personnel with 3–5 or more years of experience whereas small and medium have mostly staff with 0–3 years of experience. This makes it more difficult for SMEs to face security issues adequately. All our respondents are from the field of cybersecurity which was important for the understanding of the research and its goal. This was to make sure there are no inconsistencies in the findings as most of the respondents with a background of cybersecurity have some experience with working on such solutions.
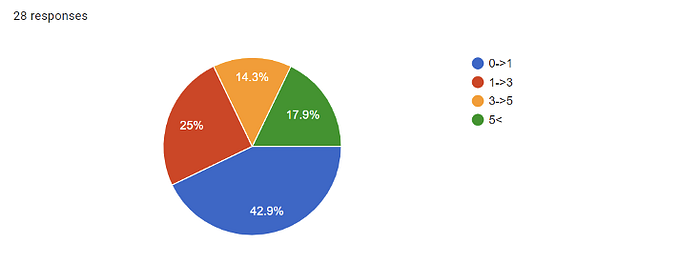
Figure 7 : Showing how many experience the personnel have in the cybersecurity domain
Question 7: Do you think traditional computing environments face problems such as visibility, availability and lack of monitoring to identify threats?
In this new age, traditional solutions create more issues rather than solve one. There are very few organisations, mostly small as can be seen from the responses that are left with no option but to employ these methods as modern solutions become infeasible.

Figure 8 : Showing how many people believe that traditional computing faces threats
Question 8: Why do you think SIEM solutions have not been adopted in many companies yet?
It was observed through the responses that most personnel from large organisations think its due to problems in technology companies do not adopt SIEM and on the other hand small organisation personnel saw budget as the main challenge. One major reason why organisations fail to have a budget for security is because they are unaware of the importance of security today. However, for small and medium organisations it is difficult to allocate budget under constraints. With the modern solutions there comes a disadvantage of use of advanced technology which requires technical know how to operate. The third most selected reason shows that there is a greater need to educate organisations about these products and their functioning.
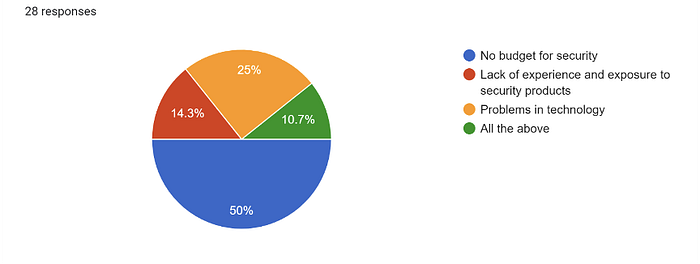
Figure 9 : Showing why SIEM solution have not been adopted in the business yet
Question 9: Do you feel that if a SIEM solution is incorporated into your network, it provides sufficient security?
There is no respondent that feels a SIEM solution could not provide sufficient solution More than half of the respondents find it to be sufficient which makes it a suitable end to end solution to test for our problem.
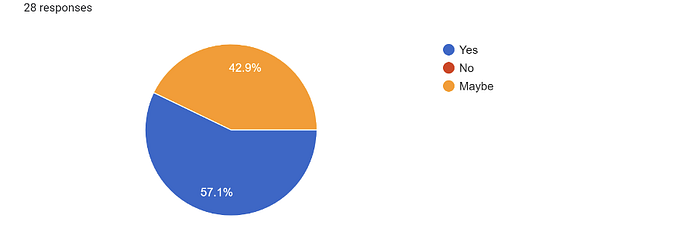
Figure 10 : Showing if SIEM is integrated will it provide sufficient security
Question 10: According to you, how long would it take to implement a SIEM solution?
Maximum responses show that it would take approximately 0–9 months to implement a SIEM solution which is a short span of time to safeguard against the ever-increasing attacks. It has also been observed that the larger the organisation the more time it will take for the solution to be implemented.
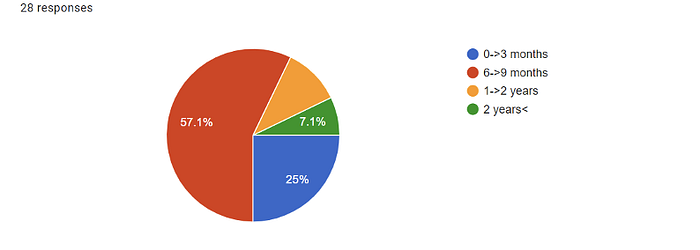
Figure 11 : Depicting how much time is taken for the SIEM implementation
Question 11: How many engineers do you think would be required to monitor and respond to security threats identified on your network?
It goes without saying, larger the organisation the more personnel required for response and vice versa. In most small enterprises they require 1–3 engineers whereas 3–5 in most medium scaled organisation and more than 5 in large organisations.
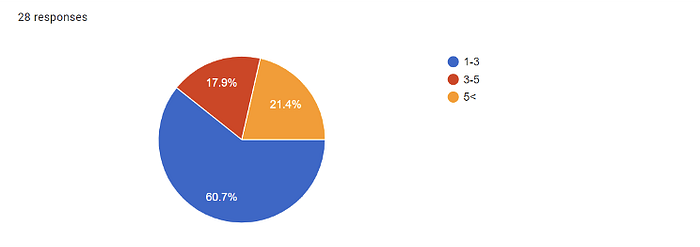
Figure 12 : Showing engineers required for the SIEM monitoring
Question 12: Based on your experience, what are the major challenges of successfully deploying and integrating a SIEM within your IT infrastructure?
The greatest issue to be addressed as it can be seen is lack of comprehensive technical knowledge within organisations. The need to hire the right staff for carrying out a smooth integration of SIEM is necessary and with this other issues can also be managed. It can be safely said from above results that to employ and operate a SIEM solution, a dedicated team is crucial.

Figure 13 : Major challenges faced with the SIEM
Question 13: Based on the information given in the diagrams, do you think Wazuh SIEM tool would enhance the security of your organisation’s IT network?*
*Respondents were briefed about Wazuh in the email sent to approach them along with a link to its official website.
With 68% of cybersecurity personnel saying that Wazuh can enhance the security, we can go ahead and set up the test and evaluation. Further results will give a clear picture if open source SIEM solutions like Wazuh are the best possible solution for security challenges faced by SMEs.
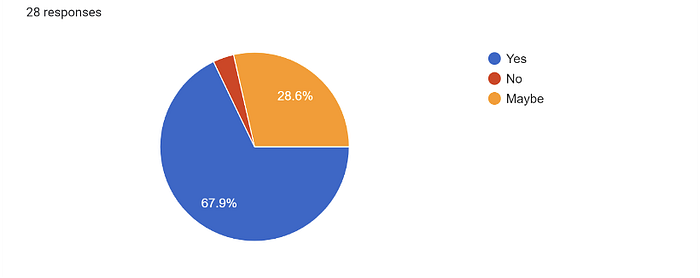
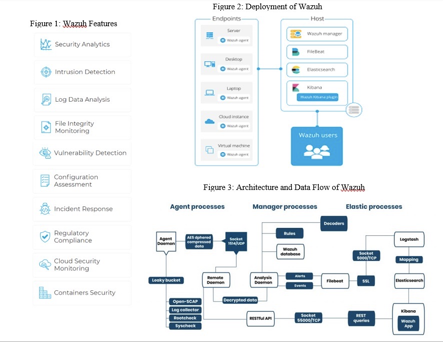
Figure 14 : Showing security personnel interest in the Wazuh SIEM
5. Technical details and artefact development
What is Wazuh?
With the assistance of the commands like curl or the web browsers, Wazuh API is built on the Restful API which helps in the interaction of the applications. There are 4 capabilities of the Wazuh API at the moment they are Manager overview, the agents management, search and the root check control. Wazuh provides a framework which keeps checks of the regulatory compliance and the incident response for the organisation. It also helps in the detection of the threats, intrusion attempts by the treat actors, user actions which are not authorised, anomalies in the system architecture etc.
Why Wazuh?
Wazuh is a thorough SIEM solution as it has all the features identified in introduction, namely event correlation, identity mapping, compliance reporting, application programming interface, situation detection (Intrusion Detection Host), rule based access control and key performance indication.
This process shows how easily Wazuh can be deployed and operated by any enterprise without incurring extra costs. It has many benefits and the main reason it is applicable most to SMEs is that It is free and open source (Macredie, R., & Mijinyawa, K.,2011, pp. 237–250). and offers functional support and technical guidance to their clients. It provides a backend that can be customised to user needs as the application of rules can be customised as per the requirements of any business by minimal personnel with working technical knowledge of cybersecurity. It helps with the interpretation of collected data and take necessary actions. It is being used many reputed companies such as Salesforce and Groupon etc.
Wazuh Architecture
Wazuh Agent
The wazuh agent is a lightweight agent which is developed to execute a variety of tasks with the aim of triggering automated incident response when a threat is detected. Following are the key functionalities of the Wazuh Agent:
· Monitoring of the policies and configuration evaluation
· Data Aggregation of all the events
· Spotting of the malicious threat actors
· Observing the traffic on the open ports of the organisation
· Keeping track of the confidentiality of the files
· Maintaining the list of all the active processes
The Wazuh agents can be installed on different end points such as Mac OS X, Solaris, Windows, AIX, HP-UX etc.
Wazuh server
All the data which is gathered by the Wazuh Agents is analysed by the Wazuh servers with the inbuilt rules and decoders with integrated cyber threat intelligence which is constantly looking for the Indicators of Compromise (IOC’s). From multiple 100’s or even 1000’s of agents, a single Wazuh server can analyse the information and also horizontal scaling can be done if it was set in the cluster mode.
The server also serves as a management tool for the agents, enabling them to be configured and updated remotely as needed. In addition, the server may issue instructions to the agents, such as triggering a response when a threat is identified.
Elastic Stack
Wazuh generates the alerts and all of them are being sent to the Elastic Search, all these alerts are stored and indexed in elastic search only. With the combination of the Kibana and Wazuh, it provides a strong frontend which enhances the user experience. The data which is being parsed from the manager to the agent can be analysed with the help of the data visualization.
Security Analytics
With the help of Wazuh SIEM we can collect, aggregate, index and analyse the data generated by the endpoints. This data helps in to determine the intrusions, anomalies and malicious events. With time, the cyber-attacks have become more advanced making difficult for the organisation to detect and mitigate them. With the help of Wazuh SIEM, the organisation can easily manage the real time threats. Wazuh Agents is a light weight program that can be installed on the endpoint to monitor all the security logs and with the help of cyber threat intelligence, data analysis can be done.
Endpoint Detection and Response (EDR)
With Wazuh in place, all the advanced threats will be monitored 24 by 7. The aim of the Wazuh SIEM is to provide in-depth visibility and detailed insights into the security events which will be investigated by the security personnel’s. Many complex payloads and exploits which cannot be detected with signature analysis by the traditional antivirus software’s, Wazuh SIEM helps them to detect the more complex malwares etc. Also, with the assistance of the Wazuh agent, a whole suspicious network patch can be blocked if it is in an attack.
Host-based Intrusion Detection System (HIDS)
Wazuh agent detects intrusions or device false usage at the host level by integrating anomaly and signature-based technologies. It also can be used to track user behaviour, evaluate security settings, and identify security flaws.
Compliance & Security Management
Wazuh implements the required security controls mandated by industry standards like PCI DSS, HIPAA, GDPR, and others. The solution collects and analyses data from a variety of sources, linking security warnings to regulatory requirements.
A comprehensive SIEM solution
Wazuh is a data collection, analysis, and correlation tool that can also be used for threat identification, enforcement management, and incident response. It can be used on-premises, in hybrid cloud settings, or in the cloud.
Intrusion Detection
Wazuh agents i.e. the endpoints Windows, Linux and Mac are monitored by the Wazuh manager which is constantly searching for the anomalies, suspicious patterns and different signatures. With the consistent data, the wazuh agent can detect the dissimilarity in the system call responses, network listeners which are not registered and help in the spotting of the hidden files. With its regular expression (regex) engine, wazuh agent uses a signature based mechanism to for the intrusion detection and monitoring for IOC’s (indicators of compromise) which will help in the investigation of the incident if any.
Log Data Analysis
All the data such as application logs etc. which is generated by the Wazuh agents is sent to a central manager for the analysis. With the rules in the Wazuh SIEM, the user have now more transparency for all the misconfigurations, malicious activities, violations in the system policy and the system errors.
File Integrity Monitoring
All the events of the file system such as changes in the permission, in the content, attributes of the file or even changes in the ownership, Wazuh help to monitor all of them. With the combination of cyberthreat intelligence, the file monitoring attribute of the Wazuh, for the determination of the threats and the hostile hosts. It also have many compliance standards such as PCIDSS etc.
Vulnerability Detection
Wazuh agents collect software inventory file and transmit it to a server, where it is compared to continually updated CVE (Common Vulnerabilities and Exposures) databases to identify recognized malicious programs. Automated risk analysis enables us to detect weak areas in your key infrastructure and take immediate measures before adversaries take advantage of them to compromise our company.
Configuration Assessment
Wazuh keeps track of device and application configuration settings to ensure they meet the security policies, specifications, and/or hardening guidelines. Wazuh Agents run scans on a regular basis to look for applications that are considered to be unstable, unpatched, or configured insecurely. Configuration tests can also be configured, which allows them to be tailored as per our business specific needs. The alerts provide suggestions for improved setup, references, and regulatory compliance mapping.
Incident Response
When such requirements are met, Wazuh offers out-of-the-box active responses to execute various defensive measures to resolve active attacks, such as disabling access to a device from the threat agent. Wazuh may also be used to conduct live forensics or incident response tasks by remotely running commands or device queries, detecting signs of compromise (an indicator of compromise), and assisting with other interactive forensics or incident response tasks.
Regulatory Compliance
In the cybersecurity space, there are many security compliances such as payment card industry data security standard (PCI DSS) etc are all integrated into the Wazuh SIEM making it easier for the small and medium enterprises more feasible to use it among the other market SIEM’s. The compliance requirements are met by Wazuh as it is combined with the multi-platform support and with its scalability feature. Multiple dashboards can be created which are used to generate reports helping in the different regulations to analyse the data.
Cloud Security
Wazuh provides API-based monitoring of cloud infrastructure, with integration modules that can extract vulnerability information from well-known cloud providers including Amazon AWS, Azure, and Google Cloud. Wazuh also includes rules for evaluating the performance of your cloud environment and quickly identifying flaws. Wazuh agents are lightweight and are available on multiplatform which can be used to keep a tab on the environment.
Containers Security
Wazuh monitors and detects risks, vulnerabilities, and anomalies in our Docker hosts and containers, providing security awareness. Users can track images, sizes, network settings, and active containers using the Wazuh agent’s native Docker integration. Wazuh gathers and analyses comprehensive runtime data constantly.
Phase 1 — Installation
Installing Wazuh and the server agent on Windows OS, configuring Virtual machine
with Kibana and Elasticsearch
Following are the steps to install Wazuh SIEM:
1. To run the WAZUH, we have to install the Oracle Virtual Box which is freely available.
2. Download Cent OS and run the following script: curl -so ~/all-in-one-installation.sh https://raw.githubusercontent.com/wazuh/wazuh documentation/4.1/resources/open-distro/unattended-installation/all-in-one-installation.sh && bash ~/all-in-one-installation.sh
3. Once the script is complete, then we can log in on the Wazuh IP address. For our case it is https://192.168.0.77. The username is root and the password is wazuh.
4. Once the installation of the Wazuh SIEM is complete in the Oracle Virtual Box, then we need to install the Wazuh Agent on our Windows 10 machine to collect the logs.
5. To add the Wazuh agent to the Wazuh Manager (SIEM), we need to run the following command /var/ossec/bin/manage_agents . Following output will be generated.
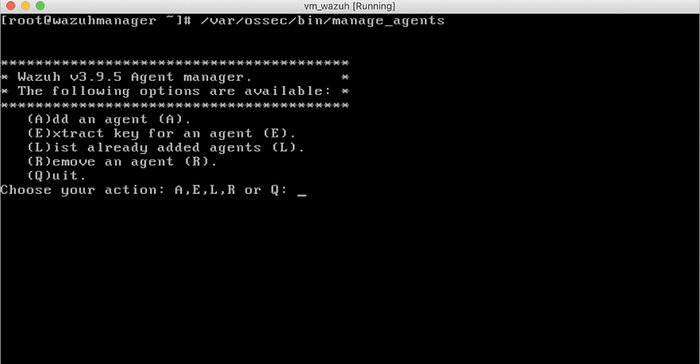
Figure 15 : Adding Wazuh agent to the Wazuh Manager
6. /var/ossec/bin/manage_agents with this command we can add the new machine to our SIEM by adding the IP address of the endpoint, give its name and an id to identify the endpoint.
7. Once added, the key has to extracted from the Wazuh Manager which has to be added to the Wazuh Agent which is present in the Windows Machine.
8. Wazuh Agent consist of two field that is IP address in which we will add the Wazuh Manager IP address (192.168.0.77) and in the second field we will add the key that is MDAyIGhhemFhIDE5Mi4xNjguMC43MSA5NWFmMzBhNjg5ZTExYzI2ZGRjMTQ3ZDk5Y2YxNzJjNDE3ZDM2MmFkZDk5NDU2MGIzMTJlMWM1MTY3NmM0ZDYw
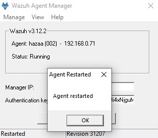
Figure 16 : Adding Wazuh agent key to the Wazuh Manager on the endpoint and restarting it
9. After adding the IP address and the Key, the status will of the Wazuh Agent will be running.

Figure 17 : Status of Wazuh Agent Manger is running
10. We have successfully added the endpoint and we can see that we have now the active device 1.
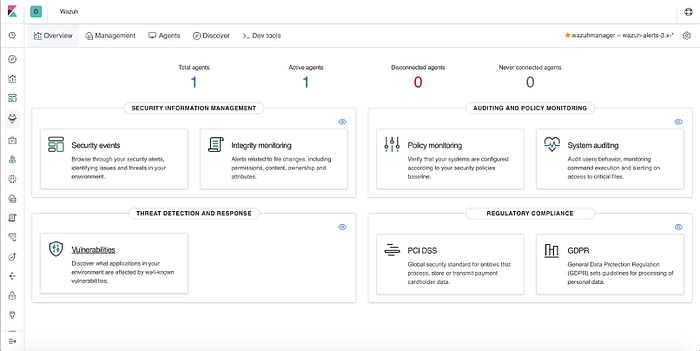
Figure 18 : Wazuh Dashboard
Configuring the Email Alerts
1. We are adding the email id varularoraalert@gmail.com in the Manage Email Groups tab of the Wazuh SIEM frontend. On this email, varularoraalert@gmail.com all the Wazuh SIEM alerts will be sent if there are rules trigger.

Figure 19 : Adding the email on which the alerts will be received
2. We have to add the email address from which the email will be sent from the Wazuh SIEM that is varularora@gmail.com. We have to configure the smtp server and have to get the details from google as we are using Gmail. The smtp server details are publicly available. In the host option, we will add smpt.gmail.com and in the port number we will add 587 number as this is being used by google. Last step, is to select the encryption mentioned that is TLS which stands for Translation Layer Security.
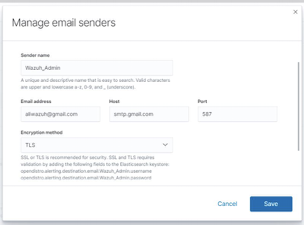
Figure 20 : Adding the email from which the alerts will be sent
3. In the alerting tab, we will add the name, we have written the name Wazuh Hazaa Security Alerts — Email. Under the settings, we will manage the senders and will choose and the last option is of the Recipients tabs in which we will add the email group that is Ali-Wazih-Email-Alert.
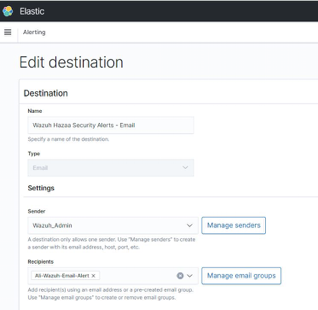
Figure 21 : Editing the destination for the email alerts
4. In this step we will add the backend configuration of the email in Elasticsearch.

Figure 22 : Backend configuration of the Elasticsearch
5. In the OSSEC configuration file, we have to change the settings such as changing no to yes of the email_notifications, chaning the email from where the email will be send an email to where the email notification will be send.

Figure 23 : Backend configuration of the OSSEC
6. We can see the screenshot of the test alert which we were able to send successfully. If any of the commands or any line we miss, then we would not be able to send even the test alert.

Figure 24 : Test Email Alert on the email
Phase 2 — Sample Log collection
We collected the logs from our Windows 10 endpoint. After few minutes we can see in the below screenshot that the data starts to flow in and all the data is automatically parsed and the bar graph is generated.
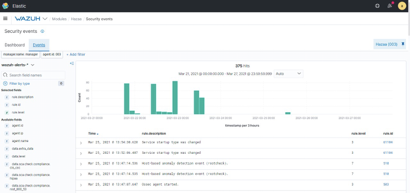
Figure 25 : Log collected shown on the dashboard
Phase 3 — Rule Application
We have taken one rule which will we demonstrate the working of the alerts in the Wazuh SIEM. For the instance we have taken Firewall Alert Trigger.
Following are the steps to configure the rules in the Wazuh SIEM, we will explain the making of one rules in detail, by replicating these steps we will make the other rules. They are as follows:
1. Under the alerting tab, we need to go to monitor, then we will create the rule name. In this instance, we are creating a rule for the Firewall state Trigger — On/Off. In the define monitor tab, we will use the Define using visual graph as we will be using the graph. In the index tab we will use * which is a wildcard and will be used in the index pattern.
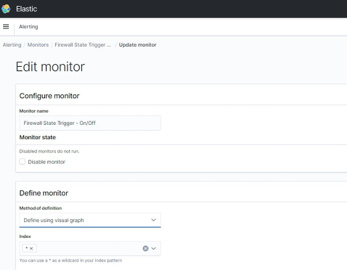
Figure 26 : Creating the test rule
2. We will add the @timestamp option in the time field.

Figure 27 : Adding the timestamp to the test rule
3. We can see that the rule has been created of the Firewall State Trigger on/off. The green line shows that no alerts has been triggered and the red line shows that alerts has been triggered.
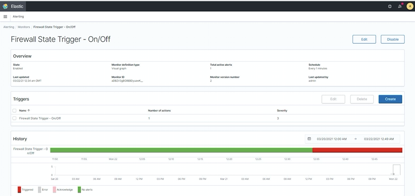
Figure 28 : Firewall test rule created
4. We can see that the firewall alert has been triggered on the basis of the rule.
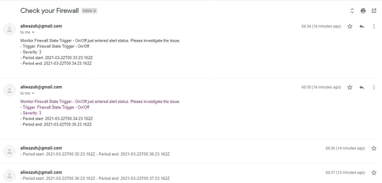
Figure 29 : Firewall Alert generated and the email is received
6. Testing and Evaluation
a) Rule 1 : Firewall Alert Trigger
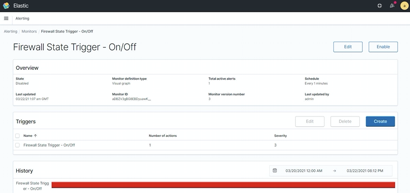
Figure 30: Firewall Alert Trigger
b) Rule 2 : Registry Value Integrity Checksum Alert Trigger
In order to control external outcomes or mask operation, enemies can insert, erase, or control data at rest. Adversaries can try to influence a business method, organisational awareness, or decision-making by manipulating stored data.
A number of file types, such as Office archives, databases, stored addresses, and special file formats, may be included in the stored data. The degree of adjustment and its effect are determined by the type of data as well as the adversary’s objectives and strategies. In order to have the desired effect on complex systems, an adversary would certainly require special skills and probably access to advanced tools relevant to the system, which would normally be gained through a lengthy information collection campaign.

Figure 31: Registry Value Integrity Checksum Alert Trigger
c) Rule 3 : Registry key Integrity Checksum Alert Trigger
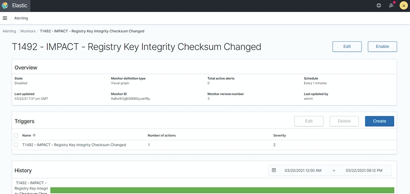
Figure 32: Registry key Integrity Checksum Alert Trigger
d) Rule 4 : Failed Attempt to Run Sudo Alert Trigger
Sudo command is the most used keyword in the linux, Mac or the Unix operating systems. The sudo command is used to elevate the privileges in the endpoints. Attackers can use perform sudo caching and they can spawn the process by getting the higher privileges. With the help of the sudo command, the user can delegate the authority to the certain group of users or even to a single user. Attackers can also exploit the defective configuration of the machine to escalate the privileges without getting the even the user’s password.
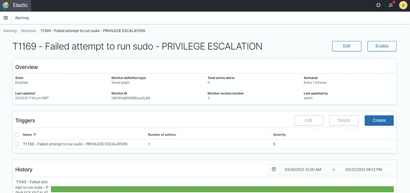
Figure 33 : Failed Attempt to Run Sudo Alert Trigger
e) Rule 5 : Multiple pre-greetings rejects Alert Trigger
Adversaries can send emails to users in order to obtain confidential material. Emails can contain confidential information, such as trade secrets or personal information, that adversaries may find useful. Email may be collected or forwarded by enemies from email systems or customers.
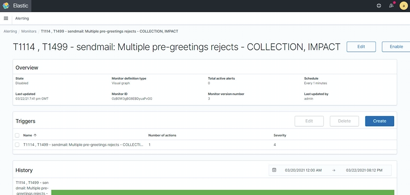
Figure 34 : Multiple pre-greetings rejects Alert Trigger
f) Rule 6 : Possible breakin attempt Alert Trigger
When credentials are uncertain or hashes are acquired, attackers can use brute force attack strategies to attract access to accounts. Without knowing the code for a specific account or collection of accounts, an attacker may use a repeated or incremental method to crack the password.

Figure 35 : Possible breakin attempt Alert Trigger
g) Rule 7 : Netscreen Firewall: Successful admin Login Alert Trigger
As a way to gain Initial Entry, Persistence, Privilege Escalation, or Defense Evasion, attackers can obtain and abuse credentials from established accounts. Breached passwords can also be used to override security controls on different resources on network networks, as well as for continuous access to wireless networks and externally accessible services. Compromised credentials may also give an attacker enhanced access to individual networks or restricted network areas. To ensure their existence difficult to track, adversaries can choose not to use malware or tools in accordance with the legitimate access those passwords offer.
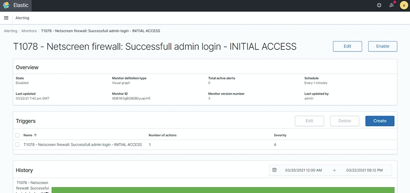
Figure 36 : Netscreen Firewall: Successful admin Login Alert Trigger
h) Rule 8 : Microsoft Event log Cleared Alert Trigger
Adversaries have the ability to remove or change created objects on a host system, such as logs or captured files like quarantined malware. Logs are stored in various locations and formats depending on the device or product, but standard operating system logs are saved as Windows events or Linux/macOS files like Bash History (/var/log).
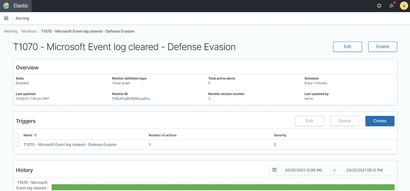
i) These activities can cause issues with event compilation, documentation etc. This could jeopardise the security of security solutions by allowing significant incidents to go unnoticed. Owing to a lack of evidence to assess what happened, this practise can also obstruct forensic investigation and incident response.
Figure 37 : Microsoft Event log Cleared Alert Trigger
j) Rule 9 : Impad Multiple Failed Logins from same source IP Alert Trigger
A block of users AD list can be compromised and being attempted to login by BOTS as a query list. Can be legit by AD admin but not preferred so on security alert at Severity 4 and Critical alert level. However, mostly it will be blocked by any security measures in place like firewall.

Figure 38 : Impad Multiple Failed Logins from same source IP Alert Trigger : Impad Multiple Failed Logins from same source IP Alert Trigger
k) Rule 10 : Courier Brute Force (Multiple Failed Logins) Alert Trigger
A course of password cracking attempt to get unauthorised login attempt to an account with dictionary passwords or guessable passwords leads to this attack. Very high at severity level and must be monitored. However, the user can be legit but process login policies will help from any false.
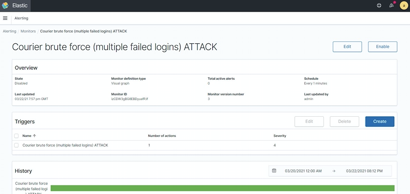
Figure 39 : Courier Brute Force (Multiple Failed Logins) Alert Trigger
l) Rule 11 : Critical CVE 2019–9169 Alert Trigger
Heap-based buffer over-read via an attempted case-insensitive regular-expression match is achieved in this CVE. This can lead to buffer overflow attack and is also required to monitor for latency-based systems where the interruptions might cause errors in the workflow.
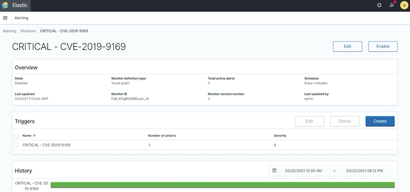
Figure 40: Critical CVE 2019–9169 Alert Trigger
Rule 12 : Critical CVE 2016–7944 Alert Trigger
Platforms might allow remote X servers to gain privileges via a length value of INT_MAX, which triggers the client to stop reading data and get out of sync which is Integer overflow attack to get injected and is a critical vulnerability.

Figure 41: Critical CVE 2016–7944 Alert Trigger
We can see in the below screenshot all the alert which has been triggered are being sent over the email.

Figure 42: Email Alerts of all the rules which triggered
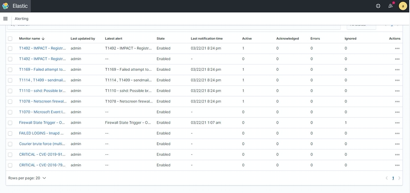
List all created alerts of the rules
Figure 43 : Rules Dashboard in the Wazuh
7. Conclusion
The implication of this project’s findings for security practitioners and SMEs are presented in this section. The chapter closes with briefly discussed limitations of the study and improvements for potential SIEM and SME related research and practice It’s difficult to see how the situation for SMEs can improve without further drastic improvements to the methods available to them, given the recognised limitations in terms of expertise, knowledge, and budget.
However the findings of this study show SIEM is a dynamic solution, if implemented properly with continuous upgrades can prove to solve all their issues SIEM systems are complex systems that involve a number of modules, security components, and interfaces. The use of such systems is correlated with significant implementation and operation efforts. As a result, these types of systems are still uncommon in small and medium-sized businesses (SME). This study focuses on open source tools which are available free of cost and provide technical support to the organisations.
The aim of this research is to suggest a realistic and useful structure for SMEs which can be used when reacting to real time data breaches. In order to alter the authorities about the live data breach response system, we conducted a series of semi-structured interviews. This SME-specific system differs from others in that it integrates successful strategies from the pre-defined checklists and the military architecture, as well as an explicit feedback loop to ensure that lessons are learned over the lifespan of the business.
It is also relatively straightforward and light-weight compared to other best practise guidelines targeted at larger organisations with more capital. This is not the final edition of the system. It is clear that SMEs must use it “in frustration” and refine and strengthen it based on their experiences.
We’re hoping to find SMEs eager to test the system and, as a result, improve it until it becomes a useful resource. We assume that deploying tried-and-true strategies from other disciplines would be beneficial in incident response as well. In the face of the upcoming GDPR regulations, our long-term goal is to better help SMEs in dealing with data breaches.
This project successfully pinpointed the security event management difficulties recognized in the SME context; highlighted these problems and attempted to solve them through the working demonstration of open source SIEM tool.
Limitations of Study
There are a few limitations of this study, first is the lack of existing research on SIEM in the context of SMEs. With almost no pretext, there was no information on response solution specific to fit in with small and medium enterprises. Most of the existing research is based on huge IT infrastructures of giant corporations.
The primary information gathered was limited to the questionnaire that were not filled out in the physical presence of researcher which raises the possibility of misinterpretation of questions hence leading to misguided data.One limitation of the study is no emphasis on the continuing improvement aspect of the SIEM tool that is a crucial step to ensure it functions beneficially. There is a serious need to create awareness amongst staff how to respond quickly to dynamic changes.
Improvement
Hopefully from this report, more practitioners in the field will be inspired to undertake more research in this particular area as the study stresses on the problems of the SMEs and lays it out in detail. From the findings of the report, a more extensive research into demonstration of SIEM tools can be carried out helping SMEs further with awareness of functions of the tool.
Furthermore, to practice continuous improvement it is suggested that as this tool is implemented, any organisation should set up meetings with concerned personnel at regular intervals to check the performance and any correctional steps required from current findings to prepare for future contingencies as a part of regular business activities.
8. References
1. O. Podzins and A. Romanovs, “Why SIEM is Irreplaceable in a Secure IT Environment?,” 2019 Open Conference of Electrical, Electronic and Information Sciences (eStream), Vilnius, Lithuania, 2019, pp. 1–5, doi: 10.1109/eStream.2019.8732173.
2. K. Detken, T. Rix, C. Kleiner, B. Hellmann and L. Renners, “SIEM approach for a higher level of IT security in enterprise networks,” 2015 IEEE 8th International Conference on Intelligent Data Acquisition and Advanced Computing Systems: Technology and Applications (IDAACS), Warsaw, Poland, 2015, pp. 322–327, doi: 10.1109/IDAACS.2015.7340752.
3. G. W. P. Chamiekara, M. I. M. Cooray, L. S. A. M. Wickramasinghe, Y. M. S. Koshila, K. Y. Abeywardhana and A. N. Senarathna, “AutoSOC: A low budget flexible security operations platform for enterprises and organizations,” 2017 National Information Technology Conference (NITC), Colombo, Sri Lanka, 2017, pp. 100–105, doi: 10.1109/NITC.2017.8285644.
4. Kapoor, K., Renaud, K. & Archibald, J. 2018. Preparing for GDPR: helping EU SMEs to manage data breaches. In: AISB 2018: Symposium on Digital Behaviour Interventions for Cyber-Securilty. AISB, pp.13–20
5. Montesino, R., Fenz, S., & Baluja, W. (2012). SIEM-based framework for security controls automation. Information Management & Computer Security, 20(4)4, 248–263.
6. Metzger, S., Hommel, W., & Reiser, H. (2011). Integrated Security Incident Management — Concepts and Real World Experiences. Sixth International Conference on IT Security Incident Management and IT Forensics (IMF). Stuttgart, Germany. May 10–12, 2011.
7. Karlzen, H. (2009). An Analysis of Security Information and Event Management Systems: The Use of SIEMs for Log Collection, Management and Analysis (Master’s Thesis). Chalmers University of Technology, University of Gothenburg, Gothenburg, Sweden.
8. Fink, D. (1998). Guidelines for the Successful Adoption of Information Technology in Small and Medium Businesses. International Journal of Information Management, 18(4), 243–253.
9. Gartner Inc. (2012). Gartner Magic Quadrant for Security Information & Event Management (2012). Retrieved June 8, 2013, from http://insight.q1labs.com/GartnerSIEMMQ2012.html.
10. Gordon, S. (2010). Operationalising Information Security — Putting the Top 10 SIEM Best Practices to work. Retrieved June 8, 2013, from http://whitepapers.theregister.co.uk/paper/view/2584/ opinfosec-siemtop10bestpractices-122210.pdf.
11. Kufel, L. (2013). Security Events Monitoring in Distributed Systems Environment. Security and Privacy, 11(1), 36–43.
12. Miller, D. R., Harris, S., Harper, A. A., VanDyke, S., & Blask, C. (2011). Security Information and Event Management (SIEM) Implementation. New York: McGraw-Hill.
13. Macredie, R., & Mijinyawa, K. (2011). A theory-grounded framework of Open Source Software adoption in SMEs. European Journal of Information Systems, 20, 237–250.
14. Department for Digital, Culture, Media and Sport. 2016. Cyber Security breaches survey. (2016). Available at: https://www.gov.uk/government/statistics/cybersecurity-breaches-survey-2017
15. Sneza Dojkovski, Sharman Lichtenstein, and Matthew Warren. 2006. Challenges in fostering an information security culture in Australian small and medium sized enterprises. In ECIW2006: proceedings of the 5th European conference on Information Warfare and Security. Academic Conferences Limited, 31–40.
16. E. Novikova, I. Kotenko: Analytical Visualization Techniques for Security Information and Event Management. 21st Euromicro International Conference on Parallel, Distributed and NetworkBased Processing (PDP), 2013, IEEE Computer Society, p. 519- 525
17. Rodrigo Werlinger, Kasia Muldner, Kirstie Hawkey, and Konstantin Beznosov. 2010. Preparation, detection, and analysis: the diagnostic work of IT security incident response. Information Management & Computer Security 18, 1 (2010), 26–42.
18. International Standards Organisations. 2011. ISO/ IEC 27035, Information technology — Security techniques — Information security incident management. (2011). https://www.iso.org/standard/44379.html
19. Experian. 2016. SMEs under threat — The crippling consequences for unprepared small to medium sized businesses. (2016). http://www.experian.co.uk/assets/identity-and-fraud/smes-under-threat.pdf
20. H.M. Government. 2015. Cyber security: advice for small businesses. (2015). https://www.gov.uk/government/publications/ cyber-security-what-small-businesses-need-to-know
21. Tawileh A., Hilton J., McIntosh S. (2007) Managing Information Security in Small and Medium Sized Enterprises: A Holistic Approach. In: ISSE/SECURE 2007 Securing Electronic Business Processes. Vieweg. https://doi.org/10.1007/978-3-8348-9418-2_35
